Unmanned vehicles, drones, offer society the promise of more effective, safer ways of performing everyday, and even unusual, tasks. Whether it’s inspecting underwater power lines, monitoring traffic, or driverless cars that simply can’t drink and drive, the idea of putting machines, rather than humans, in harm’s way is appealing. But drones also offer a new category of threats: being used for nefarious purposes that erode, rather than enhance, the security fabric of our society. Innovations are accelerating in both directions.
Rise of the Drones
From Military to Civilian Use
Drones have been active participants in military campaigns for over 150 years since the Austrians first launched two hundred pilotless balloons mounted with bombs against the city of Venice in 1849. Balloon surveillance was used in the US Civil War, kite surveillance in the Spanish-American War, and in WWII unmanned B-24 bombers loaded with explosives were flown into German bunkers. After WWII, drones were predominantly used for increasingly advanced forms of surveillance, until 2002 when the CIA armed their predator drones for unmanned attacks in Afghanistan.
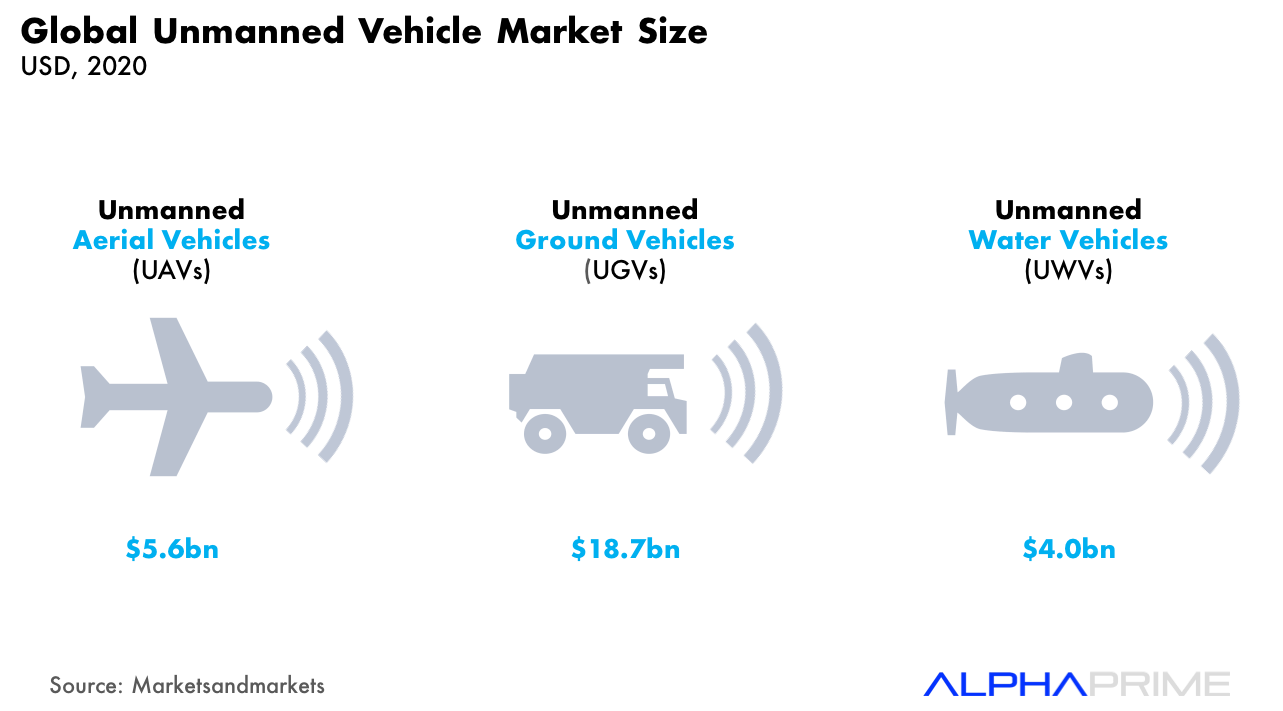
And while history has tended to overlook the commercial applications of drones (despite Nikola Tesla patenting the first remote-control for unmanned vehicles in 1893), the civilian drone industry has recently grown into a vibrant ecosystem and is projected to reach almost $30 billion in size by 2020.
Commercial Landscape
The infrastructure and agricultural industries seem set to claim almost two thirds of the commercial drone arena, driven by their need for high people mobility and high quality data. Industry experts suggest that a combination of relatively, dangerous work environments, coupled with razor thin margins, will drive a large component of current business services and labor in these two sectors to be replaced by drone-powered solutions
Drone Anatomy 101
Architecture Visualization
Before going further it’s worth refreshing on the technical architecture underpinning drone solutions:
Terminology
At the most simplistic level, UAV systems typically have 3 major components:
- The payload is the whole purpose of the UAV: whether it’s a high definition camera for surveillance, or an expendable substance like pesticide for crop dusting, this is the core item the UAV carries to perform its mission. Attached to the payload is the payload transmitter that relays signals and commands to and from receivers on the ground. Advanced UAV sensor payloads can collect a broad range of data, ranging from full-motion video (FMV) to air quality. This highly complex and compressed raw data is then recompiled, analyzed and adjusted using payload processors.
- The vehicle’s flight path is controlled from the ground control station (GCS) which contains computer systems (including navigation, command and instrument modules) that calculate and adjust commands to and from the UAV through the ground control transceiver. The GCS is supplemented with manual controllers and field engineers/ pilots who issue commands that override and supplement the GCS’s limited capacity.
- Manual and ground control commands are received by the onboard avionics system that includes a global positioning system (GPS) unit. The GPS unit communicates by radio with a “constellation” of several dozen navigational satellites that provide precise position and velocity data. Other core components of the flight computer include an inertial measurement unit which delivers sensor data on roll, pitch and yaw, combined with an onboard processor, to calculate attitude and heading. A second bank of sensors are coordinated by the integration board to determine speed, angle of approach, landing, and other sophisticated maneuvers. Finally the servo management board is part of establishing command and secure communication with the GCS, and processes and adapts the information collected from the GPS and attitude heading reference systems to enable landing and maneuvering of the craft.
About The Analysis: Our research leverages AlphaPrime’s proprietary data warehouse, Charlotte’s Web™ , that tracks thousands of companies that protect people and assets. This specific drone analysis was conducted in August and September 2016, with support from analysts Emma Yunqi Li and Matteo Cuda. Charlotte’s Web™ is the result of hours of painstaking research: from our first analyst (and the data warehouse’s namesake) Charlotte Kwon, to Matteo Cuda, Emma Yunqi Li, Nathan Coen and Marc Bove who have contributed to its data reserves over the years. We remember and remain enormously thankful.
About AlphaPrime: In an increasingly complex and dangerous world, threats to people and assets are escalating in diversity, frequency and magnitude. The need and ability to anticipate and respond to these threats is essential and universal. AlphaPrime invests in companies that address this need, and manage and protect people and assets. It’s not part of what we do, it’s everything we do.
Copyright 2017, AlphaPrime Management LLC